Axioms | Free Full-Text | On the Application of the Block Hybrid Methods to Solve Linear and Non-Linear First Order Differential Equations

Sensors | Free Full-Text | Application of Pulse Compression Technique in High-Temperature Carbon Steel Forgings Crack Detection with Angled SV-Wave EMATs

Blockchain-based Intrusion Detection System of IoT urban data with device authentication against DDoS attacks - ScienceDirect

PDF) Higher order stable generalized finite element method for the elliptic eigenvalue problem with an interface in 1D | Quanling Deng - Academia.edu

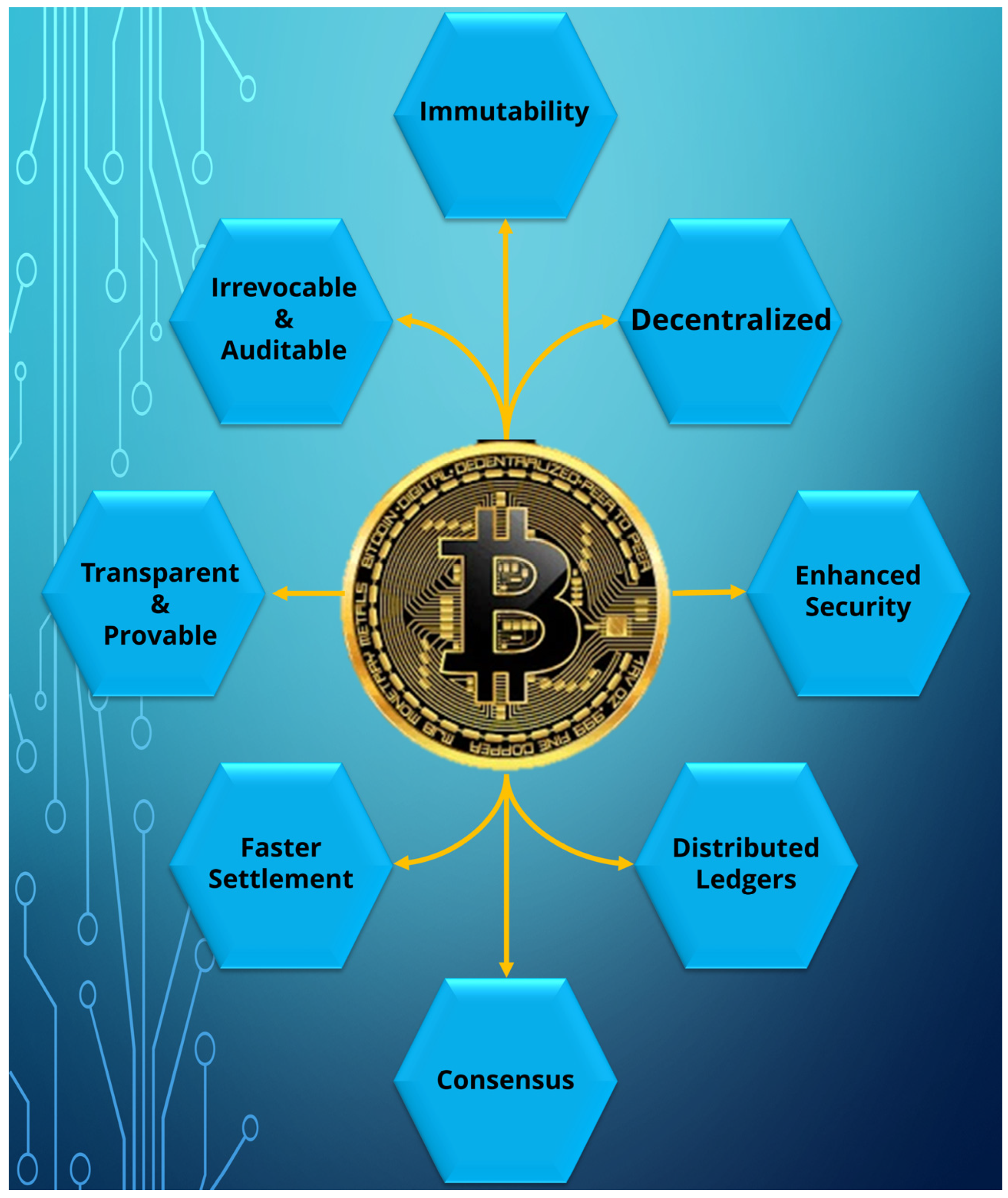
Sensors | Free Full-Text | Secure Data Transfer Based on a Multi-Level Blockchain for Internet of Vehicles

Numerical results for () s with nonnegative s. Table shows the number... | Download Scientific Diagram

Symmetry | Free Full-Text | A New Conservative Hyperchaotic System-Based Image Symmetric Encryption Scheme with DNA Coding
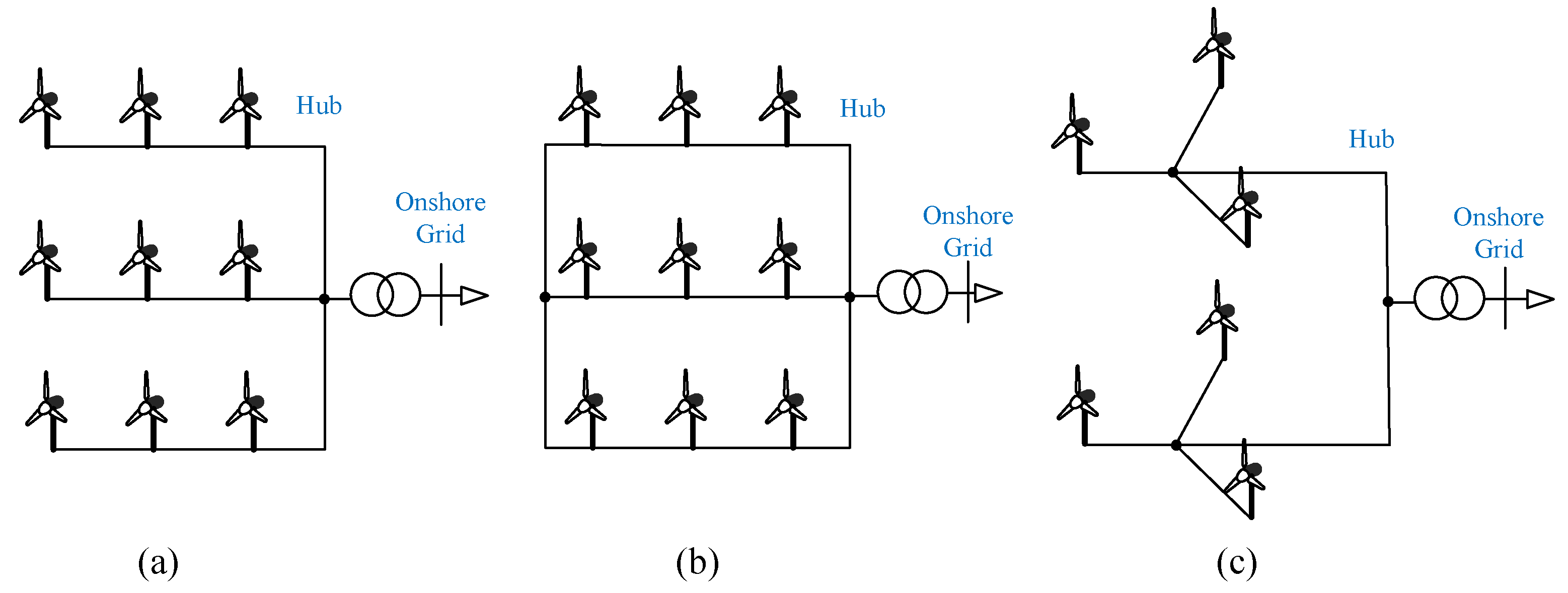
Symmetry | Free Full-Text | Small-Signal Stability of Multi-Converter Infeed Power Grids with Symmetry

BCALS: Blockchain‐based secure log management system for cloud computing - Ali - 2022 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library

Privacy‐preserving blockchain‐based contract signing with multi‐party supervision - Zhang - Transactions on Emerging Telecommunications Technologies - Wiley Online Library

SENSIBLE: SEquestered aNd SynergIstic BLockchain Ecosystem - Kshirsagar - Engineering Reports - Wiley Online Library

Filter Specifications and Approximation Theory (The Mathematical Approach to the Approximation Problem) | SpringerLink
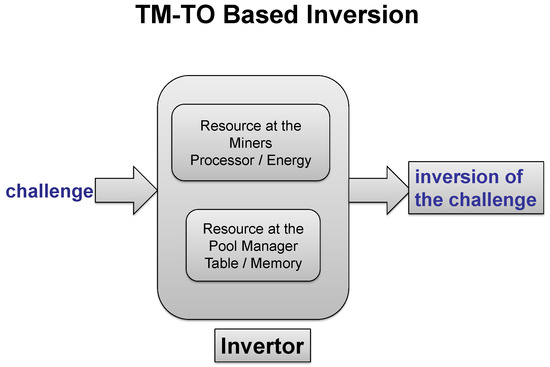
Symmetry | Free Full-Text | An Approach for Blockchain Pool Mining Employing the Consensus Protocol Robust against Block Withholding and Selfish Mining Attacks
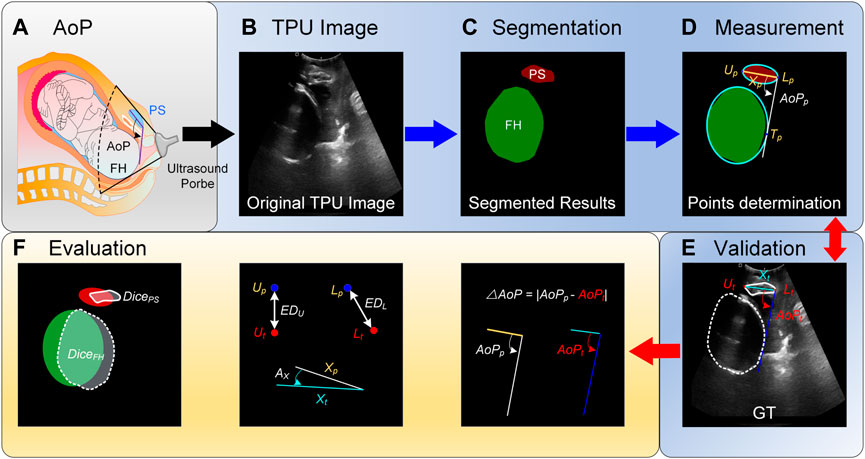
Frontiers | A framework for computing angle of progression from transperineal ultrasound images for evaluating fetal head descent using a novel double branch network